Digital transformation is a process transformation. It is driven by innovation, by changing behaviors, by looking at the value chain from different perspectives. It also constitutes perceiving new forms of risks, both as threats and opportunities, and adapting to them.
Margaret Hamilton was software developer from MIT. She developed the code for Apollo Guidance Computer in 60’s.
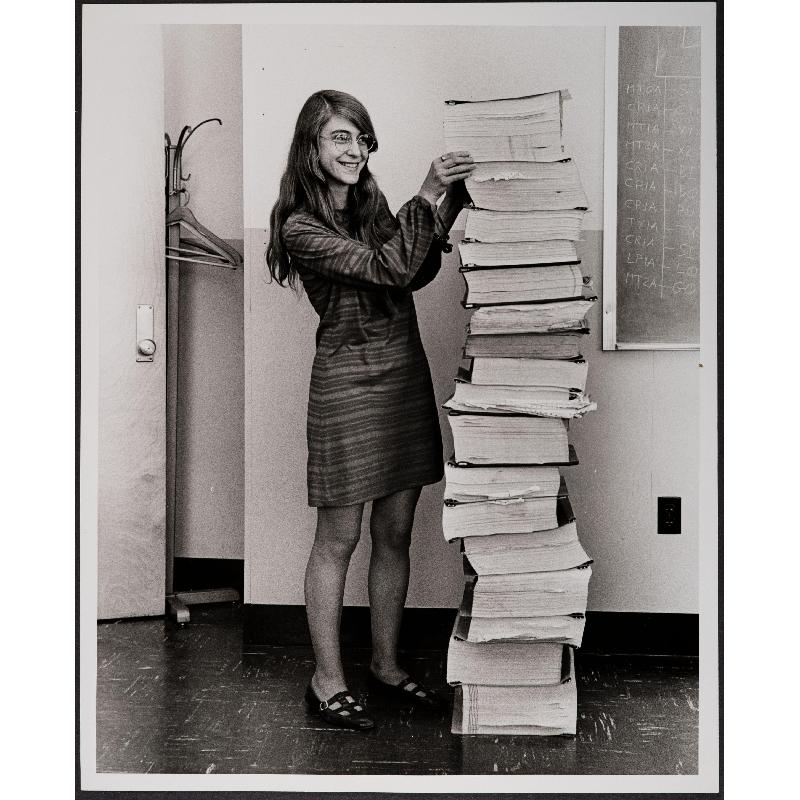
Margaret Hamilton with Apollo Guidance Computer software.
Courtesy MIT Museum.
Development of this innovative machine and procedures were result of a decade long collaboration between NASA and MIT.
“Fly-by-wire” digital computer pilot assistants were experimental since late 50’s. Their development lead to Apollo guidance computer, the most advanced digital system in aviation industry in 60’s. It required adapting landing procedures, and hence adapting pilots training. But humans had never landed on the Moon before Apollo 11 in July 1969. It was a challenge for Ms. Hamilton and her team to envisage all possible difficulties that the system could face during the Moon landing. The system was designed to augment human capacities, and not to replace them. Therefore, it had switches to override the automatic mode, and turn back to the manual mode.

Apollo 11 Guidance Computer
Credits: Computer History Museum
In unforeseen scenarios of Moon landing, a new risk materialized. A combination of computer’s process priority scheduling and utilization of different instruments/sensors during landing resulted in “Error 1202”- resource over-utilization. The approach radar was feeding too much data to the computer. The error was recognized by Jack Garman, NASA computer engineer, who informed the flight controller Steve Bailes. They weighted the risk, and proposed alternative landing procedures to astronauts. Just 6000ft over the Moon surface, Neil Armstrong switched the radar to manual mode, which reduced data flow throughput and allowed continuing the landing procedure. They landed with remaining 98kg of fuel, enough for the way back. That remains in history.

Margaret Hamilton in Apollo 11 landing module – “Eagle”
Courtesy MIT Museum.

Apollo 11, July 1969
Credits: NASA
RSA SecureID tokens were based on one of the first public-key crypto systems in 90’s, Rivest-Shamir-Adleman. They protected, and still do, many business information systems that require robust identification and identity provisioning. Implementation of this solution allowed creation of new digital services in many industries. In 1996, Adam Shostack published the paper on the critical vulnerability in the mutual authentication between ACE/Server and SecureID clients. Temporary workaround solutions were proposed as well as protocol remedies. Security administrators modified work practices on which stateless protocols to allow outside of internal networks. That mitigated risk from external threats. For mitigating internal threats more robust work practices had to be developed until the modified mutual authentication protocol was implemented by Secure Dynamics.

The United Nations Compensation Commission, where I worked from 1994 to 2005 as a system analyst, developed claims payment tracking system to support the process for compensation of 2.7 million claims worth 352.5 billion USD. The system was Web based, and SecureID tokens were distributed to governments world-wide to be able to securely access it with two-factor authentication. Implementation of RSA SecureID tokens solved several issues. Firstly, the risk of passwords breaches was reduced. Secondly, risks of user ID provisioning when authentication factors are intangible, such as “something you know”. When users are not designated directly by the organization that manages the process but rather by an external entity, then the tangible authentication factor adds the notion of possession, and inherently increases protection by the users and their organization.
However, the vulnerability outlined in Shostack’s paper required risk mitigation plan. Additional controls were installed such as firewall segregation of each module of the multi-tier system as well as the network intrusion detection system with continuous monitoring. Implementing this system required changing work practices for data management and provisioning, for identity management and customer relations, for training and risk awareness.

UNCC’s multi-tier Web-based claims payment tracking system
The above two case studies both illustrate that the adoption of emerging technologies requires business process changes, require change of work practices, and sometimes even changing corporate culture.
